Introduction
A crypto-asset wallet is a tool that allows users to interact with blockchain networks. Such wallets can be classified into hot (online) and cold (offline) wallets. Hot wallets usually consist of software wallets, whereas cold wallets consist of hardware and paper wallets. For security purposes, multiple cryptographic methods are used to open wallets and transfer coins.
How different types of encryption work
Encryption methods can be broadly divided into three categories: hash functions, symmetric encryption, and asymmetric encryption.
A hash function is any mathematical function that takes data of any length as input and maps it into a fixed-size string of values. Hash functions do not produce any decryption keys; therefore, these functions are one-way functions, making it almost impossible to decrypt the original input from the output.
As an example of this function, when a hash for the word “bitcoin” is created using a SHA256 algorithm, the string “6b88c087247aa2f07ee1c5956b8e1a9f4c7f892a70e324f1bb3d161e05ca107b” is generated as output. The SHA256 algorithm will always produce the same hash output for the same input, a change as minor as capitalising1 initial letter in the input will change the output dramatically. Readers can try hashing their data here.
Symmetric encryption is a process that generates and uses a single key to encrypt and decrypt data. It is called symmetric c as the same key is used to perform both functions. As an example, a key that moves 3 alphabets forward for encryption and 3 alphabets backwards for decryption will easily decrypt the word elwfrlq to bitcoin.
Let us consider a scenario where Alice and Bob privately send messages to each other. To do this securely using a symmetric cryptography method, they will generate a single key and share it with each other. Bob (sender) will use that key to encrypt the message and send it to Alice. On receiving the message, Alice will use the same key to decrypt the message.
Asymmetric encryption or public-key encryption is a process that generates and uses a pair of related cryptographic keys, one public and one private, to encrypt and decrypt data and protect it from unauthorized access or use. The public key is simply the hashed output of the private key. (We invite readers to watch a very insightful video on public-key cryptography). As hash functions are one-way functions, it is impossible2 to decipher private keys from public keys. A public key can be used by any person to encrypt a message so that it can only be deciphered by the intended recipient with their private key. A private key or secret key is shared only with the owner of the key.
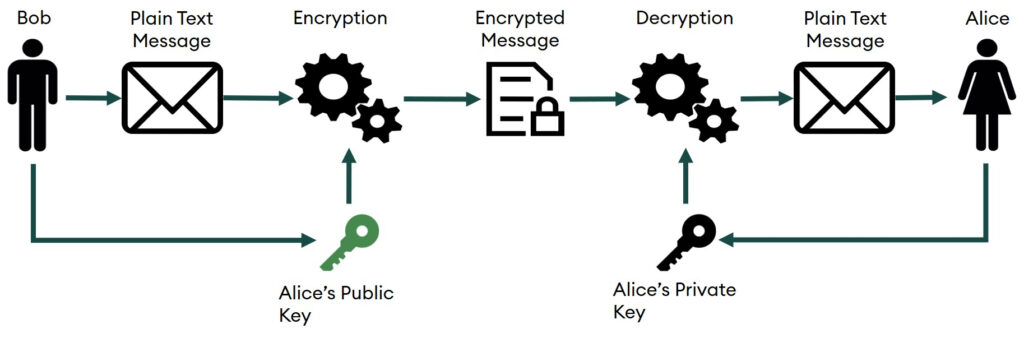
Let us consider a scenario where Alice and Bob privately send messages to each other. To do this securely, using an asymmetric cryptography method, they will generate two pairs of private and public keys, of which one pair will be with Alice and the other will be with Bob. The public key is available for all to view, so both Alice and Bob can look at each other’s public keys. However, the private key is kept as a secret by its owner. As shown in figure 1, to send a message to Alice, Bob will encrypt the message by using Alice’s public key and then send it to Alice. On receiving the message, Alice can use her private key to decrypt Bob’s message.
Figure 1: How Asymmetric Cryptography Works
How wallet encryption works
Now that we know what asymmetric encryption is, we can further understand how blockchain wallets work. Whenever a person creates a crypto-asset wallet, the wallet randomly generates3 a private key and a public key. The public key is then input into a hashing algorithm to create the wallet address of the account holder. Wallet addresses are generally 34-digit alphanumeric codes that function in the same manner as an email address. If someone intends to send cryptocurrency, such as bitcoin, to another person, they should know the receiver’s wallet address. When the bitcoins are transferred between two parties, the coins never actually leave the blockchain but merely move from one address to another.
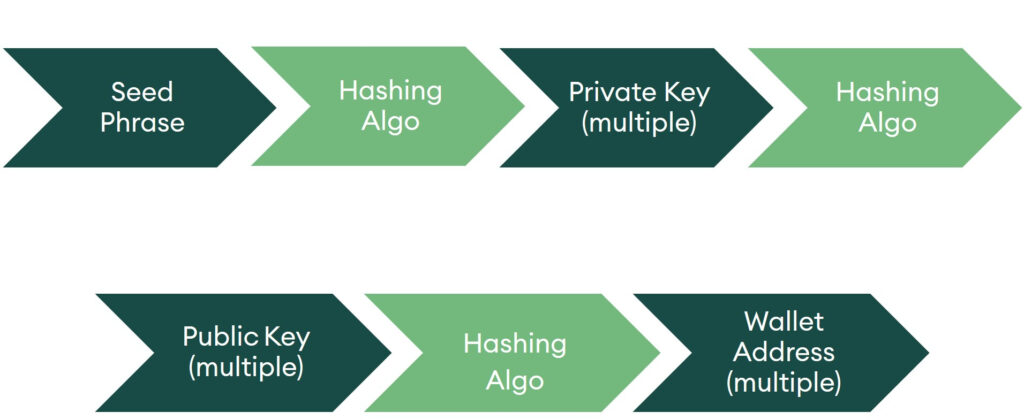
On the other hand, the private key is used to digitally sign4 new transactions and provide access to the funds in the wallet; therefore, it should not be shared with anyone. In very simple terms, it is equivalent to your password or a PIN. For easier private key management, most modern wallets generate a seed phrase out of which the private keys can be recovered. Seed phrases are a list of words that store all the information needed to get access to the wallet. The process of using the seed phrase to recover funds is shown in figure 2. One can only move from the seed phrase towards the wallet addresses and not the other way round, due to the hash function’s one-way nature. If the seed phrase is lost, the funds are almost impossible to recover. It is best practice to store both your seed phrase and private keys offline in a safe location, as anybody who has the seed phrase or private keys can access and control the wallet.
Figure 2: How Crypto-Asset Wallets Create Addresses Using Asymmetric Encryption
Types of crypto-asset wallets
There are many ways to classify a wallet. The two most common ways are based on the physical status and the operational structure of the wallet. Depending on their physical status, the majority of crypto-asset wallets can be classified as software, hardware, or paper wallets. Each type offers some advantages and disadvantages over the others (figure 3).
Figure 3: Different Types of Crypto-Asset Wallets According to Physical Status
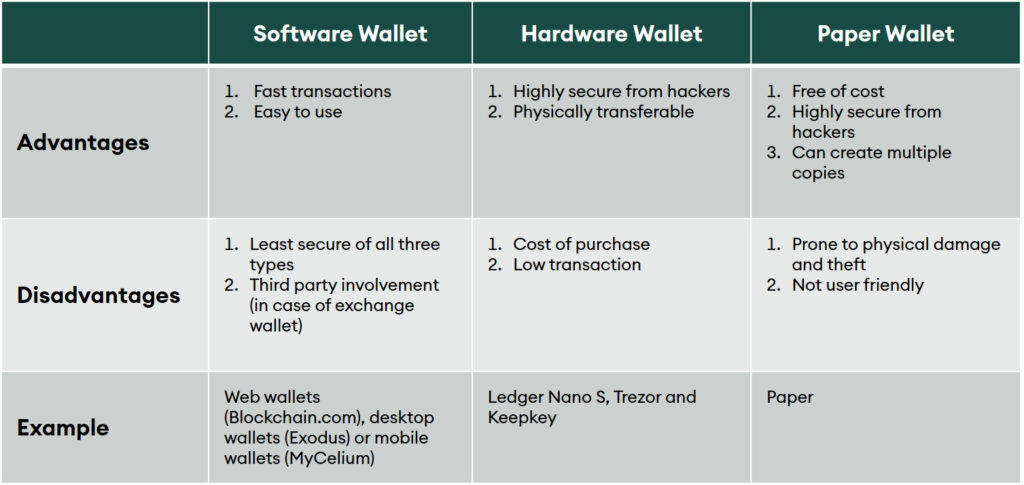
In operational terms, wallets can be classified as either hot or cold. A hot wallet is a wallet that is connected to the internet. Most software wallets fall under the hot wallet category. These provide users with the ability to quickly transfer or exchange their funds; however, they are relatively more vulnerable to attacks (or being threatened by hackers) through the internet. On the other hand, cold wallets store the users’ funds in a device that is not connected to the internet, making them more secure than hot wallets. Most hardware wallets and all paper wallets fall under this category.
Conclusion
Crypto-asset wallets use multiple types of encryption techniques to keep user funds safe. As the cryptoverse has expanded, so have the types of wallets and their security. The users of crypto assets should clearly understand the importance of things such as seed phrases, private keys, and the hot and cold nature of wallets to make well-informed decisions about storing their funds.
1bitcoin = 6b88c087247aa2f07ee1c5956b8e1a9f4c7f892a70e324f1bb3d161e05ca107b Bitcoin = b4056df6691f8dc72e56302ddad345d65fead3ead9299609a826e2344eb63aa4 ↵
2Formally speaking, it is almost impossible, as the likelihood to decipher private keys from public keys. The probability is 1 over 2128, or 1 chance in 340,282,366,920,938,463,463,374,607,431,768,211,456. (https://www.quora.com/How-does-a-supercomputer-decrypt-the-private-key-from-a-public-BTC-address-Is-that-worth-to-do) ↵
3The wallet generates multiple pairs as a security measure; therefore, a wallet can have multiple pairs of private and public keys, but to keep it simple, we’ll assume just one pair. ↵
4Digital signature is a way of authenticating a transaction. To understand more, please click the following link. https://www.tutorialspoint.com/cryptography/cryptography_digital_signatures.htm ↵